S.3982 and the Future of AI-Driven Identity Fraud Prevention
As of May 2026, the digital asset industry has reached a regulatory and technical tipping point. While the GENIUS Act…
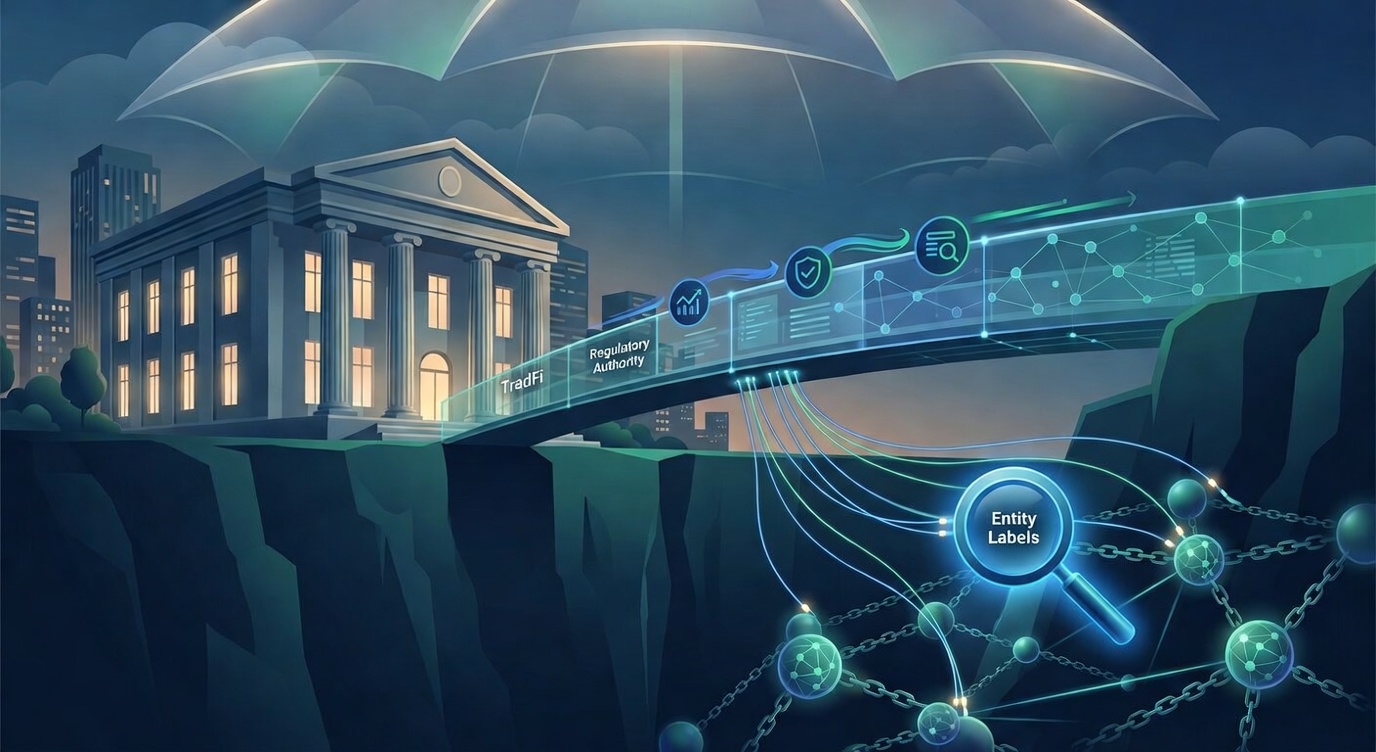
As of May 2026, the digital asset industry has reached a regulatory and technical tipping point. While the GENIUS Act forced stablecoin issuers to modernize their forensic monitoring, a more insidious threat has emerged at the point of entry: Synthetic Media. The introduction of the S.3982 – AI Fraud Accountability Act in the U.S. Senate…